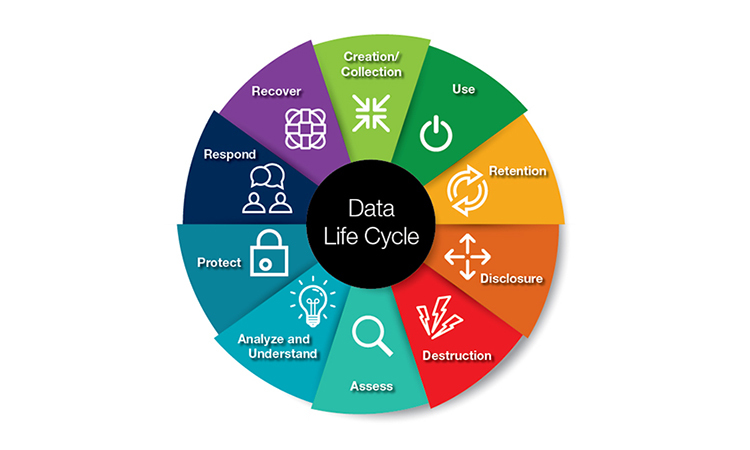
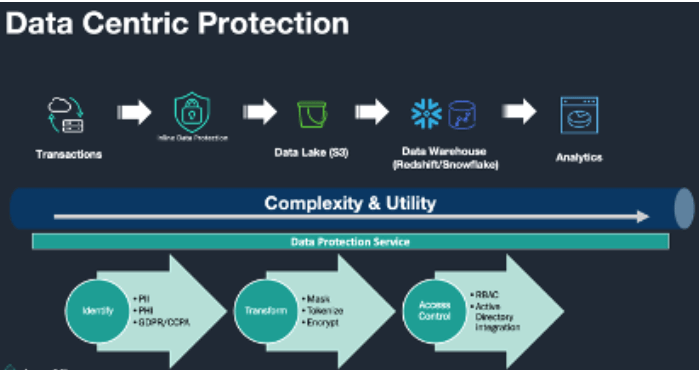
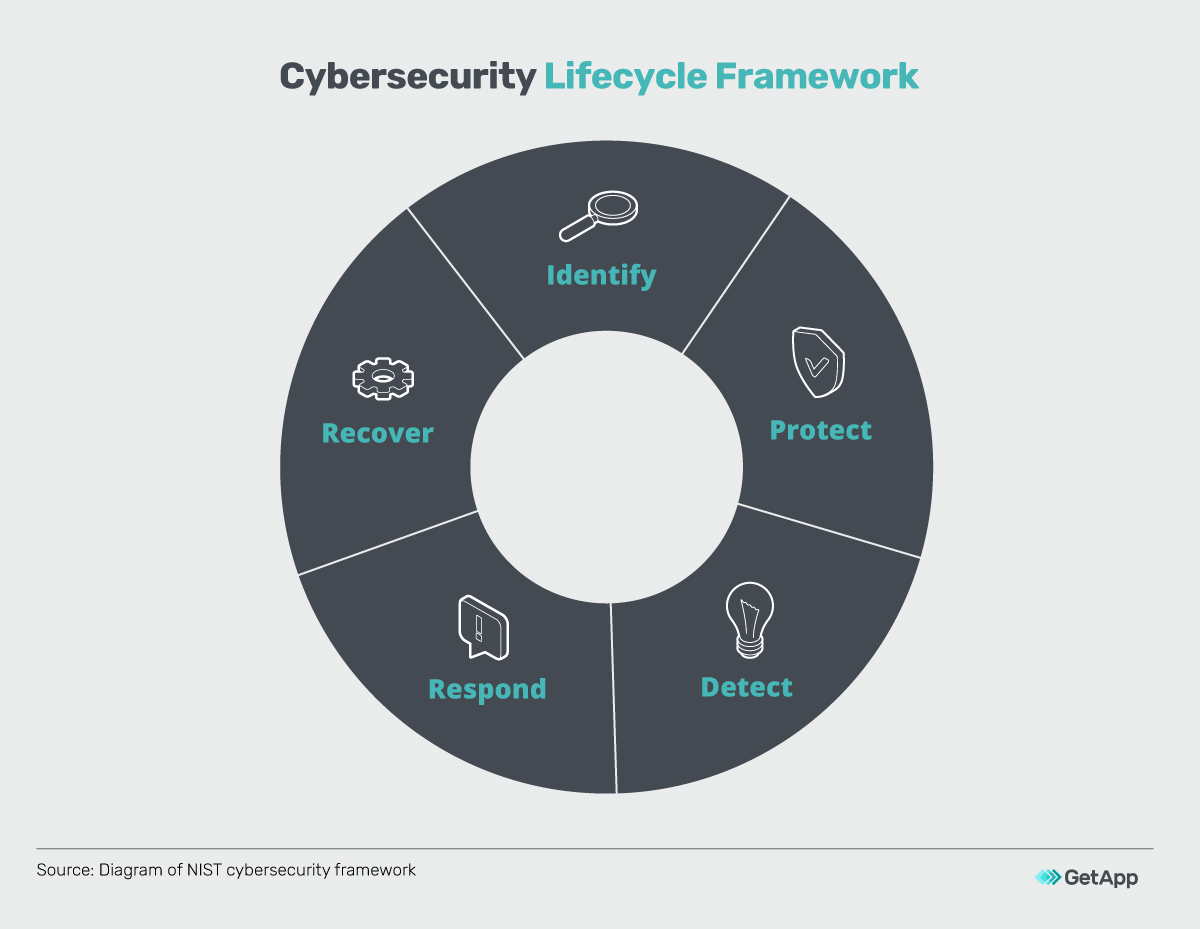
Understanding the Data Lifecycle and Five Ways to Ensure Data Confidentiality | Spiceworks It Security
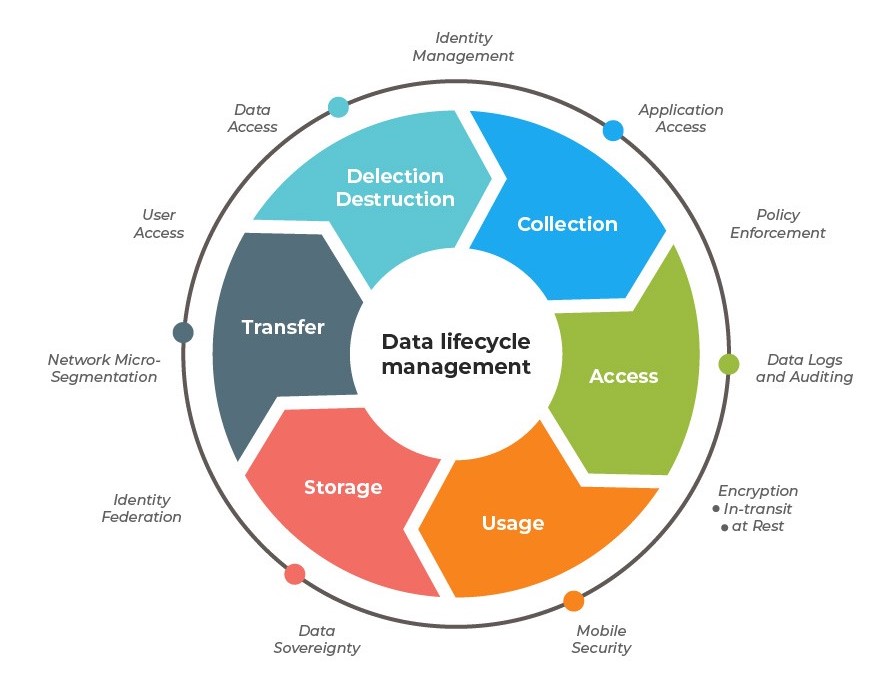
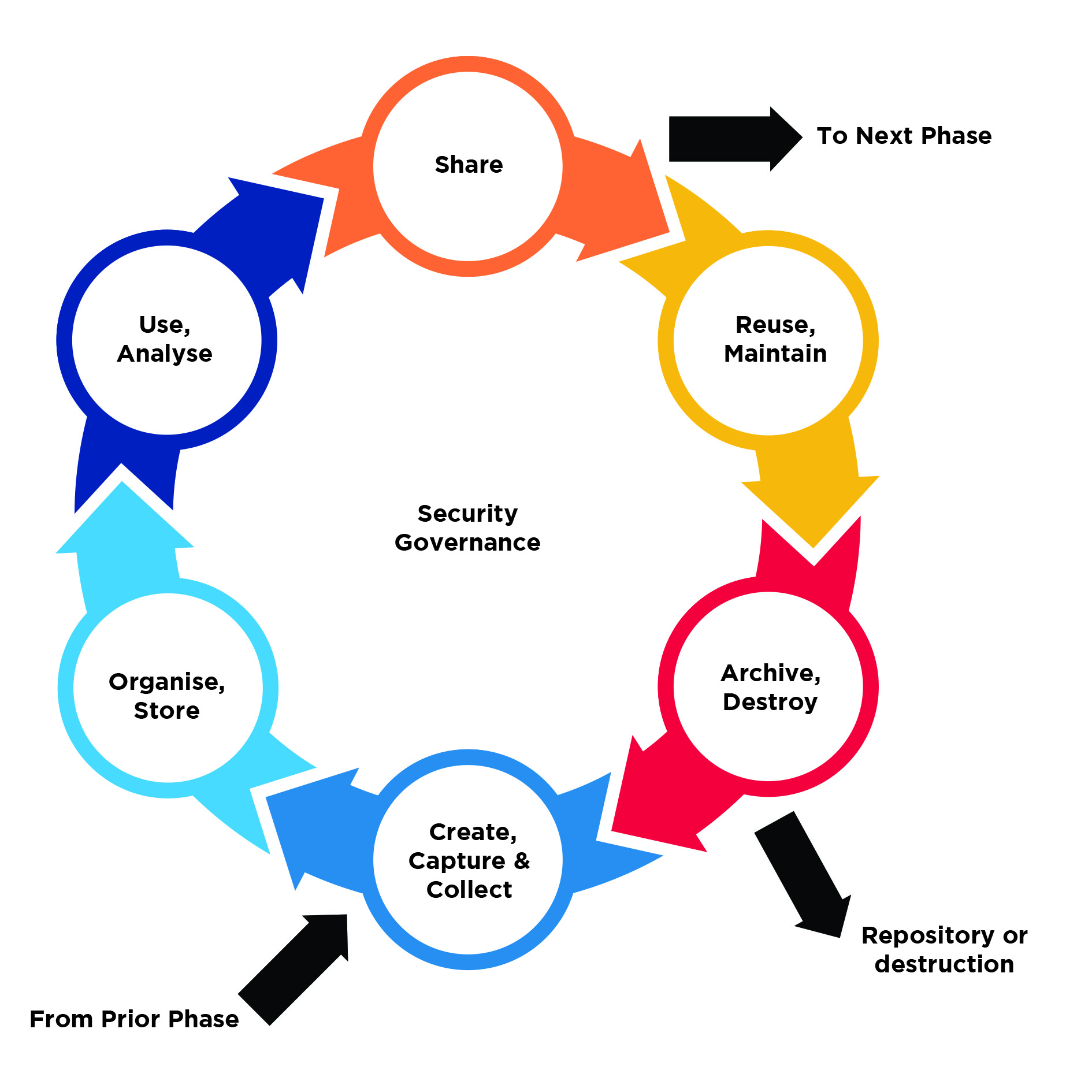
Data lifecycle management (DLM) - a solution to increase an efficiency in data management according to the Person Data Protection Act (PDPA) - ADD+ Leader in IT Asset Disposal in Asia









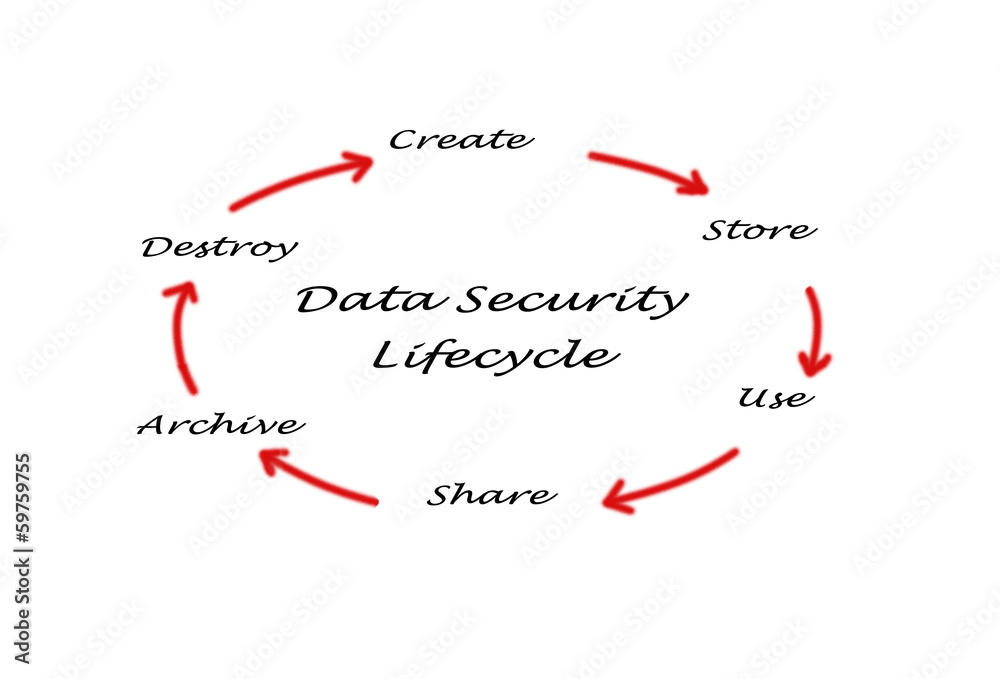


![Data Security Lifecycle [20] | Download Scientific Diagram Data Security Lifecycle [20] | Download Scientific Diagram](https://www.researchgate.net/publication/266892424/figure/fig2/AS:669227325341710@1536567636858/Data-Security-Lifecycle-20.png)