PDF) Application of Message Security Application Using Vigenere Cipher Algorithm Utilizing One Time Pad (OTP) Algorithm as a Key Generator | Akbar Iskandar - Academia.edu
![PDF]Mật Mã Học - Ocw.Mit.Edu - Ronald Rivest - Mit6_857s14_Lec03 Encryption, Perfect Secrecy, One-Time Pad.Pdf PDF]Mật Mã Học - Ocw.Mit.Edu - Ronald Rivest - Mit6_857s14_Lec03 Encryption, Perfect Secrecy, One-Time Pad.Pdf](https://s2.cuuduongthancong.com/pdfimg/mat-ma-hoc/mit6_857s14_lec03-encryption,-perfect-secrecy,-one-time-pad.pdf/mit6_857s14_lec03-encryption,-perfect-secrecy,-one-time-pad.pdf-1.jpg)
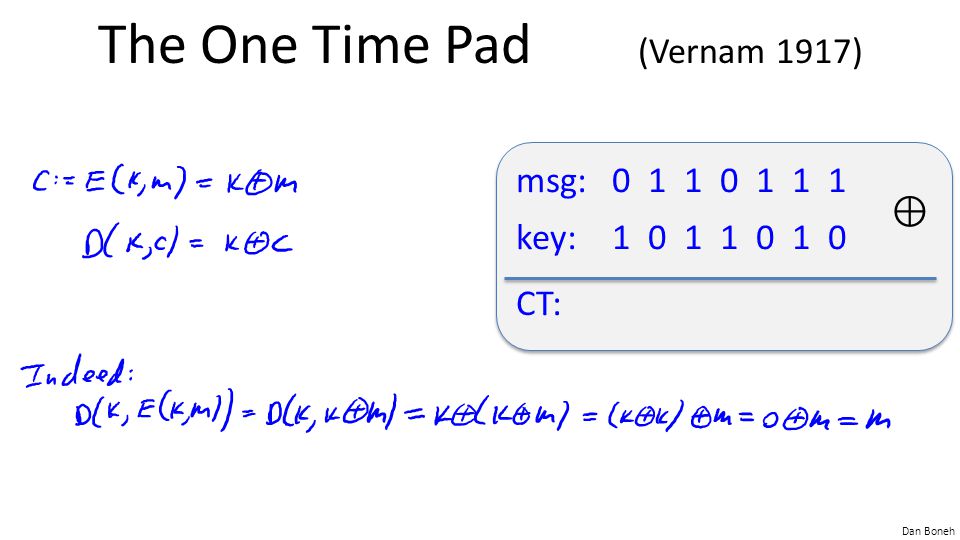
PDF]Mật Mã Học - Ocw.Mit.Edu - Ronald Rivest - Mit6_857s14_Lec03 Encryption, Perfect Secrecy, One-Time Pad.Pdf
How could quantum computing be used to create unbreakable encryption and improve security for online transactions? - Quora
Critical Thinking Assignment 3-6 - Critical Thinking 3-6: One-Time Pad (OTP) Research Use the - Studocu